Unless you’ve been living under a rock you already know the guy behind WikiLeaks, who was living at an Ecuadorian embassy in London, was recently arrested and now facing extradition to the United States – the country I’m originally from – and the country which forces tax payers to fund the second-largest stockpile of nuclear weaponry ever created.
But perhaps you didn’t know that WikiLeaks was at one point hosted by Amazon. Yep, right up until political pressure caused them to take it down. Afterall, nothing says freedom like a fear of misbehavior in a country with the highest incarceration rate in the entire world. I suppose Julian Assange’s situation could be worse… Maybe, had he also been practicing Falun Gong in China. But I digress. And there’s no telling what’s going to happen.
The Internet is free. It’s universal. When data makes its way online, whether it be Intellectual Property, Revenge Porn or Nyan Cat memes there it is. It’s out there now. For better or worse. And since Sir Tim Berners-Lee invented the WWW some 30 odd years ago existing power structures seem to have struggled since man learned to clothe their naked bodies online using strong cryptography. To this day, governments are still trying to prevent their own citizens covering their naked bodies with regard to their data online (except maybe the EU).
As humans evolve beyond our Sapien roots and reptilian instincts there’s going to be a page missing from the history books when we look back at the political censorship and despotic repression which occurred in the so-called “Modern World”.
But like I said, data on the Internet is free. And just like your data – and until there are stronger social norms online – it’s up for grabs to the highest bidder. So clothe yourself. You’ve been running around naked and the only people who actually seem to care are:
- Capitalists interested in extorting you for private gain
- Communists interested in extorting you for public gain
- Libratarians interested in helping you hide your ass online
Lucky for you I’m the latter so in this post I will guide you step-by-step on how to set-up Manjaro Linux – even on a MacBook – to connect to the ZeroNet Web using Tor for anonymity. I’ll also explain how to obfuscate Tor usage using a WireGuard VPN tunnel. When you’re finished you’ll have a new pair of cryptographic clothing almost as hot as a pair of see-through yoga pants.
You should get started now. For if you choose to wait, privacy may never come to you. Instructions to cover your naked body online may be found below.
Running ZeroNet with Tor
Complete these steps to get ZeroNet up-and-running with Tor on Manjaro Linux.
Inspect packages
Whereas Tor is available via the officially-supported community repository, ZeroNet must be downloaded and installed from the community-driven
Arch User Repository (AUR). Run pamac info zeronet in a terminal to verify:
Name : zeronet
Version : 0.6.5-1
Description : Decentralized websites using Bitcoin crypto and the BitTorrent
network.
URL : https://zeronet.io/
Licenses : GPL2
Repository : AUR
Depends On : python2 python2-gevent python2-msgpack
Optional Dependencies: tor
Maintainer : redfish
First Submitted : 17/01/16
Last Modified : 18/02/19
Votes : 63
Observe the repository, vote count, license and optional dependencies:
-
For AUR packages the number of Votes serves as popularity metric. When a package becomes popular enough it may be moved into the Arch
communityrepository and become an officially supported package. See AUR on ArchWiki for more info. -
Since the Initial commit ZeroNet has used a GPL license, meaning it considers itself to be “free software” as defined by the Free Software Foundation.
-
Tor, an anonymizing overlay network, is an optional dependency. Tor exists in the official community repository and receives TU Signatures and support.
If desired, run pamac info tor to view Tor’s repository, license, check for TU signature and view its own dependencies. You should see output like:
Expand to view output
Name : tor
Version : 0.3.5.8-1
Description : Anonymizing overlay network.
URL : https://www.torproject.org/
Licenses : BSD
Repository : community
Size : 11,8 MB
Depends On : openssl libevent bash libseccomp
Optional Dependencies: torsocks: for torify
Packager : Lukas Fleischer <lfleischer@archlinux.org>
Build Date : 23/02/19
Signatures : YesYou may also wish to search for and get info on WireGuard (WG) packages at this point. Run pamac search wireguard to list WG-specific packages for inspection.
Once you’ve finished package inspection you may continue.
Install Tor
Run the following to begin Tor installation:
pamac install tor
Press Enter when prompted to skip installation of optional dependencies. When prompted to Commit transaction type y followed by Enter to continue, then authenticate with your current user and wait while the installation finishes.
Confirm installation with pamac info tor. You should see something like:
Expand to view sample output
Name : tor
Version : 0.3.5.8-1
Description : Anonymizing overlay network.
URL : https://www.torproject.org/
Licenses : BSD
Repository : community
Size : 11,8 MB
Depends On : openssl libevent bash libseccomp
Optional Dependencies: torsocks: for torify
Packager : Lukas Fleischer <lfleischer@archlinux.org>
Build Date : 23/02/19
Install Date : 01/05/19
Install Reason : Explicitly installed
Backup files : /etc/tor/torrc
/etc/tor/torrc-distConfirm Install Date and Install Reason are as expected, then continue.
Build ZeroNet from AUR
With Tor installed, run the following to build ZeroNet from AUR:
pamac build zeronet
You will be prompted to edit the build file like:
Preparing...
Cloning zeronet build files...
Checking zeronet dependencies...
To build (1):
zeronet 0.6.5-1 AUR
Edit build files ? [y/N]
When prompted, press y followed by Enter to review the build script and make any changes desired (optional). Exit the file editor when you’re finished.
Once you’re satisfied with build files commit the transaction, authenticate and wait for the build to complete. You should see output like:
Expand to view sample build output
Building zeronet...
==> Making package: zeronet 0.6.5-1 (Rab 01 Mei 2019 06:26:29 WITA)
==> Checking runtime dependencies...
==> Checking buildtime dependencies...
==> Retrieving sources...
-> Downloading v0.6.5.tar.gz...
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 128 0 128 0 0 83 0 --:--:-- 0:00:01 --:--:-- 83
100 2701k 0 2701k 0 0 13642 0 --:--:-- 0:03:22 --:--:-- 10217
-> Found zeronet.conf
-> Found zeronet.service
==> Validating source files with sha256sums...
v0.6.5.tar.gz ... Passed
zeronet.conf ... Passed
zeronet.service ... Passed
==> Extracting sources...
-> Extracting v0.6.5.tar.gz with bsdtar
==> Entering fakeroot environment...
==> Starting package()...
==> Tidying install...
-> Removing libtool files...
-> Purging unwanted files...
-> Removing static library files...
-> Compressing man and info pages...
==> Checking for packaging issues...
==> Creating package "zeronet"...
-> Generating .PKGINFO file...
-> Generating .BUILDINFO file...
-> Adding install file...
-> Generating .MTREE file...
-> Compressing package...
==> Leaving fakeroot environment.
==> Finished making: zeronet 0.6.5-1 (Rab 01 Mei 2019 06:29:55 WITA)
==> Cleaning up...
Resolving dependencies...
Checking inter-conflicts...
Checking keyring... [1/1]
Checking integrity... [1/1]
Loading packages files... [1/1]
Checking file conflicts... [1/1]
Checking available disk space... [1/1]
Installing zeronet (0.6.5-1)... [1/1]
Configuring zeronet...
>>> Default mode is clearnet+Tor. Give zeronet permissions to configure hidden service:
>>> sudo usermod -a -G tor zeronet
>>> Add/edit the following options in /etc/tor/torrc:
>>> ControlPort 9051
>>> DataDirectoryGroupReadable 1
>>> CookieAuthentication 1
>>> CookieAuthFileGroupReadable 1
>>> CookieAuthFile /var/lib/tor/control_auth_cookie
>>> Restart tor (reload not enough):
>>> sudo systemctl restart tor
>>> Run daemon and check status and view log:
>>> sudo systemctl start zeronet
>>> sudo systemctl status zeronet
>>> sudo journalctl -u zeronet
>>> NOTE: all operations including editing zerosite files,
>>> should be done as user zeronet and config must be passed
>>> for data directory to be selected to /var/lib/zeronet:
>>> sudo -u zeronet python2 zeronet.py --config_file /etc/zeronet.conf ...
>>> OR
>>> sudo su - zeronet
>>> cd /opt/zeronet
>>> python2 zeronet.py --config_file /etc/zeronet.conf ...
Running post-transaction hooks...
Reloading system manager configuration... [1/2]
Arming ConditionNeedsUpdate... [2/2]
Transaction successfully finished.Upon build completion, follow the instructions output:
-
Run to give ZeroNet permission to configure Tor hidden service:
sudo usermod -a -G tor zeronet -
Add or edit the following options in /etc/tor/torrc file:
DataDirectoryGroupReadable 1 CookieAuthentication 1 CookieAuthFileGroupReadable 1 CookieAuthFile /var/lib/tor/control_auth_cookie -
Start ZeroNet daemon, and check its status and log:
sudo systemctl start zeronet sudo systemctl status zeronet sudo journalctl -u zeronetRun each of the above commands sequentially. Status may take a moment to appear. The log will contain the history and persist daemon status over time.
Note: If you see a connection refused error for TorManager, ignore for now.
Once you’ve tested starting Zeronet run sudo systemctl stop zeronet to shut it down. Notice, by default, the ZeroNet shutdown process takes approximately 90s for a graceful shutdown. If you’re running Tor, shut that down too.
Build Tor Browser from AUR
Adapt the steps from the last section to pacman build tor-browser. Once installed no configuration is required. Do not install any plug-ins or add-ons.
Start Services
ZeroNet and Tor can be run as system services (units) managed by systemd. Do do so we’ll use systemctl to start each, checking their respective statuses.
First start Tor and check its status:
sudo systemctl start tor && \
sudo systemctl status tor
You should see tor.service as active (running) like:
● tor.service - Anonymizing Overlay Network
Loaded: loaded (/usr/lib/systemd/system/tor.service; disabled; vendor preset: disabled)
Active: active (running) since Tue 2019-04-30 19:20:27 UTC; 18ms ago
Main PID: 7554 (tor)
Tasks: 1 (limit: 4915)
Memory: 21.7M
CGroup: /system.slice/tor.service
└─7554 /usr/bin/tor -f /etc/tor/torrc
Check systemctl status tor a few times until you see Bootstrapped 100%: Done at the bottom of the output. Then start ZeroNet and check its status too:
sudo systemctl start zeronet && \
sudo systemctl status zeronet
You should see zeronet.service as active (running) like:
● zeronet.service - Decentralized websites using Bitcoin crypto and the BitTorrent network
Loaded: loaded (/usr/lib/systemd/system/zeronet.service; disabled; vendor preset: disabled)
Active: active (running) since Tue 2019-04-30 19:23:43 UTC; 21ms ago
Main PID: 7652 (python2)
Tasks: 1 (limit: 4915)
Memory: 4.5M
CGroup: /system.slice/zeronet.service
└─7652 python2 zeronet.py --config_file /etc/zeronet.conf
In addition you should see a Web interface URL:
[17:30:29] Ui.UiServer --------------------------------------
[17:30:29] Ui.UiServer Web interface: http://127.0.0.1:43110/
[17:30:29] Ui.UiServer --------------------------------------
Navigate to the above URL in Tor Browser to access ZeroNet:
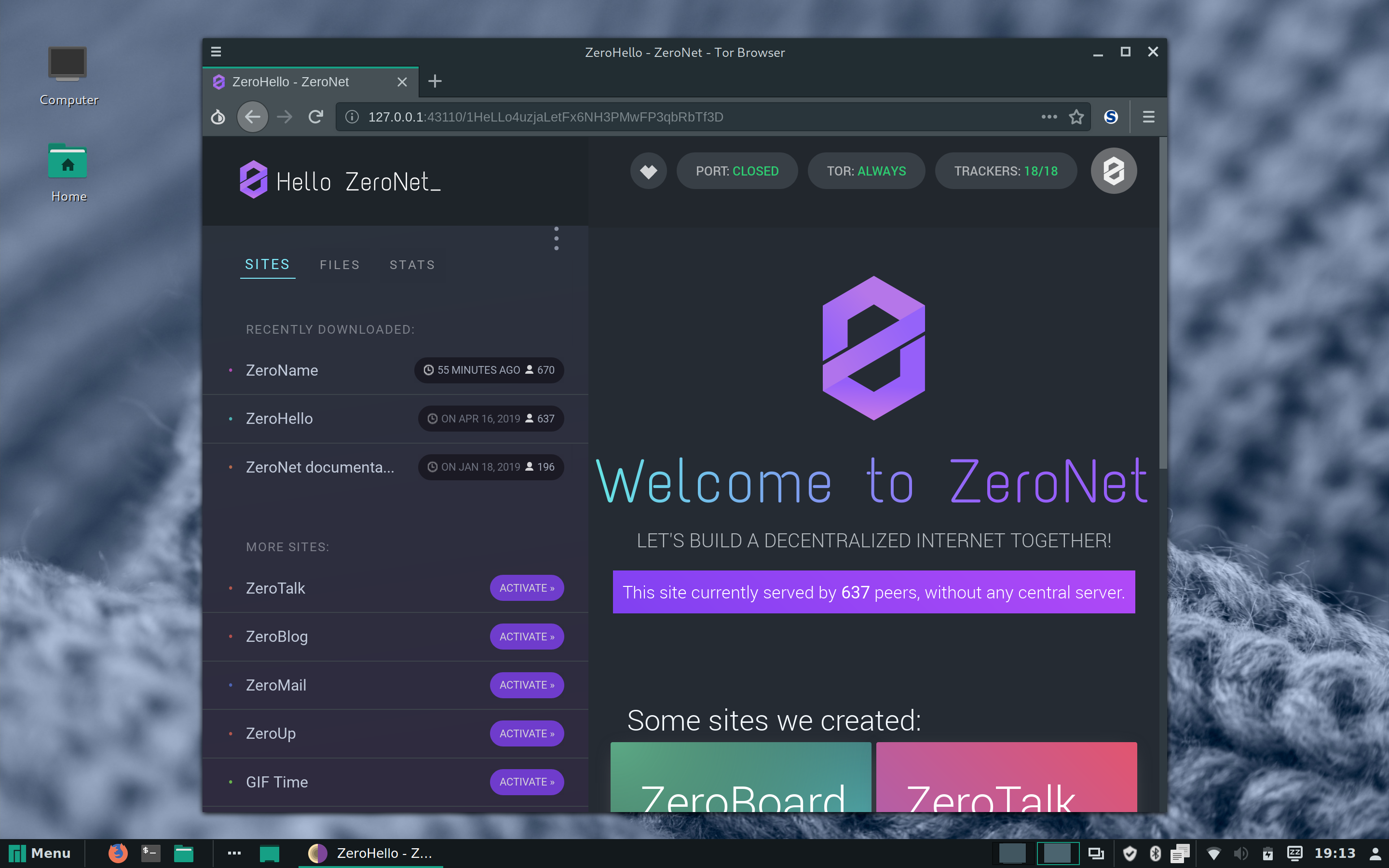
See the Troubleshooting section if you don’t see the ZeroHello welcome page. Once you’re on ZeroNet, you are now free to surf the uncensorable Web.
Troubleshooting
If you cannot pull up the ZeroHello site in Tor Browser be sure you’ve configured the browser as described in the official ZeroNet FAQ.
If you see TOR: ERROR in the ZeroHello masthead upon opening the site, click the pill button surrounding the text and follow the official instructions provided. When configured properly the following NetZero status is what you should see:
[19:23:44] TorManager Connecting to Tor Controller 127.0.0.1:9051
If ZeroNet stops working run systemctl status zeronet to check if the service is running. If its not running, restart it described in Start Services.
Using Tor Inside a WireGuard Tunnel
Traditional VPN technologies like OpenVPN and IPSec run in userland, use the TCP protocol and, as a result, are considerably slower than VPN tech like WireGuard. Due to the sluggishness of older VPN tech it hasn’t been very practical to use Tor over an encrypted connection – until now. To additionally secure your connection with WireGuard see this post for WireGuard set-up instructions.
ArchWiki docs on Transparent Torification suggest Tor only supports TCP. However, when passing first through a UDP WireGuard tunnel Tor is possible and, based on my personal experience, about as fast as Tor without Wireguard.
When you learn stuff like this you may start questioning the motives behind articles stating WireGuard is “unproven” or not “industry standard”. After all, the same was said of Telegram up until Russia banned it ostensibly because they couldn’t crack the encryption algorithm and Durov wouldn’t share the keys.
Resources
Leverage the following for more information:
